Microsoft Security Administration(MS-500) Case Study-4
Overview
You have a Microsoft 365 E5 subscription that uses Microsoft Endpoint Manager.
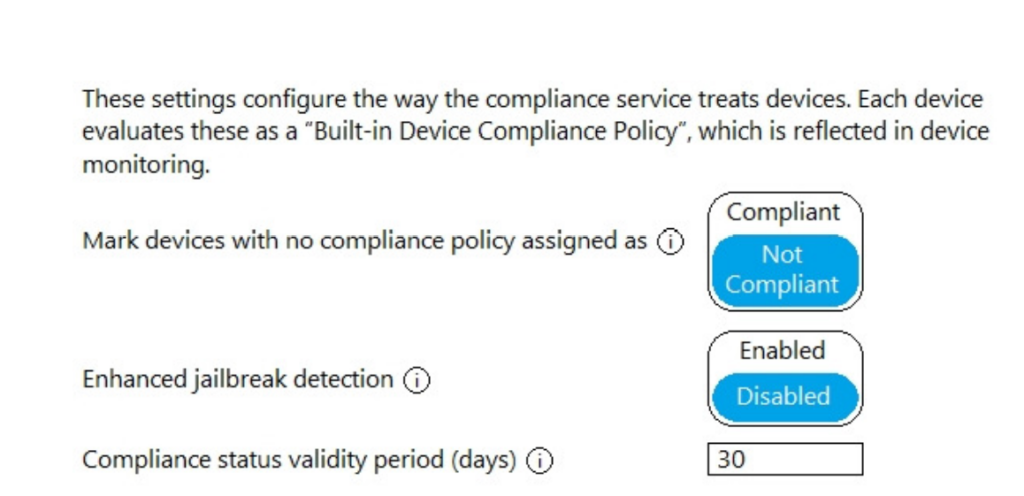
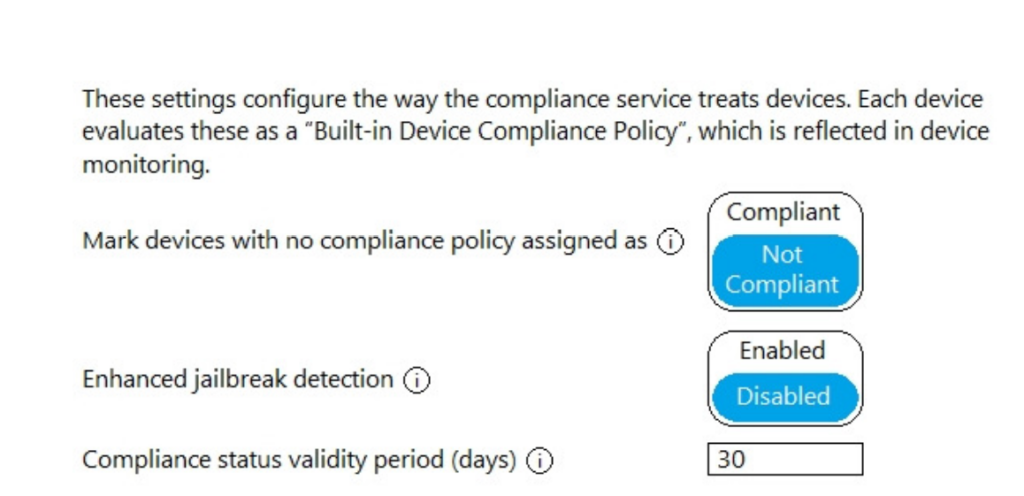
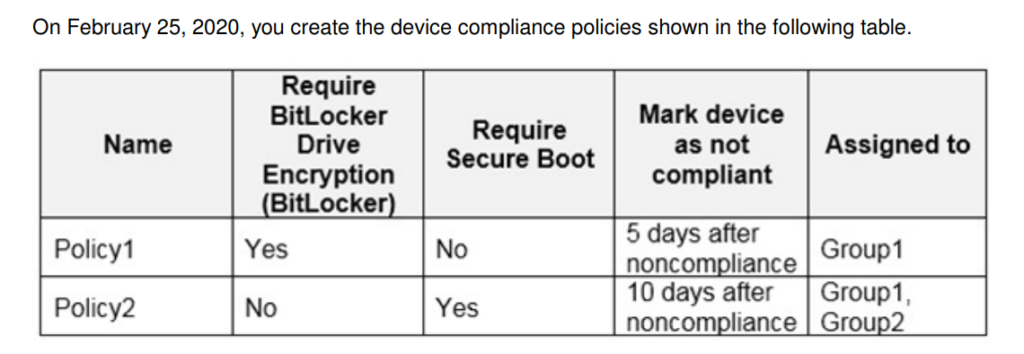
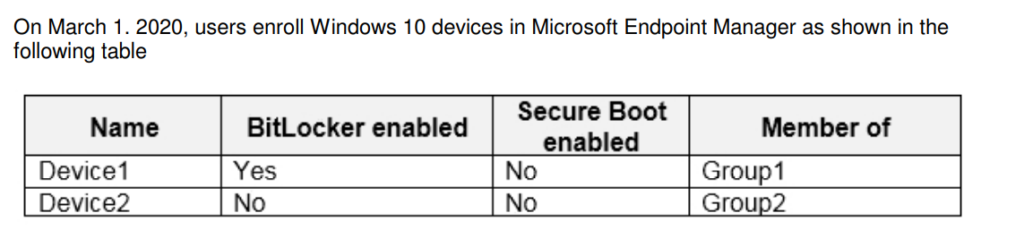
The Compliance policy settings are configured as shown in the following exhibit.
You have a Microsoft 365 E5 subscription that uses Microsoft Endpoint Manager.
The Compliance policy settings are configured as shown in the following exhibit.

Here’s the updated blog post with an increased usage of transition words to improve the flow and meet SEO readability guidelines: Simplify Device Deployment with Windows Autopilot in Microsoft Intune Managing devices efficiently has become a top priority for IT teams, especially with the rise of remote and hybrid work environments. Windows Autopilot, when paired…
So, you think your IP Address is not known to the public on the internet, you are not quite 100% correct. There are ways people on the internet and people who intend to do so can capture your IP address if they have some technical knowledge. Your Internet Service Provider is not the only one…

If you’re using Microsoft Copilot to work smarter, faster, and more creatively, learning how to manage your conversations can make a huge difference. Copilot not only responds to your prompts in real time—it also remembers past conversations, helps you pick up where you left off, and lets you organize or share your chats effortlessly. In…
Overview Fabrikam, Inc. is a manufacturing company that sells products through partner retail stores. Fabrikam has5,000 employees located in offices throughout Europe. Existing Environment Network Infrastructure The network contains an Active Directory forest named fabrikam.com. Fabrikam has a hybrid MicrosoftAzure Active Directory (Azure AD) environment.The company maintains some on-premises servers for specific applications, but most…
Overview Fabrikam, Inc. is a manufacturing company that sells products through partner retail stores. Fabrikam has5,000 employees located in offices throughout Europe. Existing Environment Network Infrastructure The network contains an Active Directory forest named fabrikam.com. Fabrikam has a hybrid Microsoft Azure Active Directory (Azure AD) environment. The company maintains some on-premises servers for specific applications,…
Overview Contoso, Ltd. is a consulting company that has a main office in Montreal and two branch offices in Seattleand New York.The company has the offices shown in the following table. Contoso has IT, human resources (HR), legal, marketing, and finance departments. Contoso usesMicrosoft 365. Existing Environment Infrastructure The network contains an Active Directory domain…
When I initially left a comment I seem to have clicked on the -Notify me when new comments are added- checkbox and from now on every time a comment is added I recieve four emails with the exact same comment. Perhaps there is a means you can remove me from that service? Kudos!
I would like to thank you for the efforts youve put in penning this website. I really hope to check out the same high-grade content by you later on as well. In truth, your creative writing abilities has encouraged me to get my very own website now 😉
Itís nearly impossible to find educated people in this particular subject, however, you seem like you know what youíre talking about! Thanks